Search Results for author: Ana Goulart
Found 2 papers, 0 papers with code
A Firewall Optimization for Threat-Resilient Micro-Segmentation in Power System Networks
no code implementations • 26 Jun 2023 • Abhijeet Sahu, Patrick Wlazlo, Nastassja Gaudet, Ana Goulart, Edmond Rogers, Katherine Davis
These protocols are vulnerable to cyber threats that power systems, as cyber-physical critical infrastructure, must be protected against.
Multi-Source Data Fusion for Cyberattack Detection in Power Systems
no code implementations • 18 Jan 2021 • Abhijeet Sahu, Zeyu Mao, Patrick Wlazlo, Hao Huang, Katherine Davis, Ana Goulart, Saman Zonouz
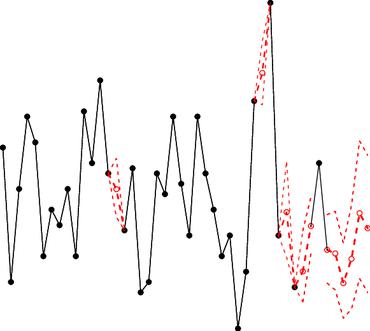
We perform multi-source data fusion for training IDS in a cyber-physical power system testbed where we collect cyber and physical side data from multiple sensors emulating real-world data sources that would be found in a utility and synthesizes these into features for algorithms to detect intrusions.