Search Results for author: Zhaohao Wang
Found 3 papers, 0 papers with code
Comparison research on binary relations based on transitive degrees and cluster degrees
no code implementations • 25 Jan 2022 • Zhaohao Wang, Huifang Yue
Finally, we provide some methods to compare binary relations by means of the transitive degree and the cluster degree.
Exploiting Spin-Orbit Torque Devices as Reconfigurable Logic for Circuit Obfuscation
no code implementations • 8 Feb 2018 • Jianlei Yang, Xueyan Wang, Qiang Zhou, Zhaohao Wang, Hai, Li, Yiran Chen, Weisheng Zhao
Circuit obfuscation is a frequently used approach to conceal logic functionalities in order to prevent reverse engineering attacks on fabricated chips.
Emerging Technologies Cryptography and Security
Spintronics based Stochastic Computing for Efficient Bayesian Inference System
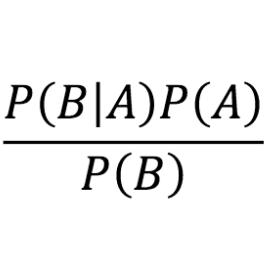
no code implementations • 3 Nov 2017 • Xiaotao Jia, Jianlei Yang, Zhaohao Wang, Yiran Chen, Hai, Li, Weisheng Zhao
Bayesian inference is an effective approach for solving statistical learning problems especially with uncertainty and incompleteness.